




































Asus Zenbook 14 New Colors Steal the Show at Computex 2026 At Computex 2026, Asus unveiled a refreshed version of its popular Zenbook 14, and this...
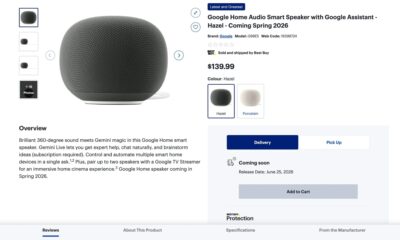

Google’s First New Smart Speaker in Six Years: Release Date Leaked via Best Buy Canada After years of silence, Google’s next-generation smart speaker may finally have...


AI Turns to Historical Secrets: Decoding Centuries-Old Papers and Hidden Letters Artificial intelligence is no longer just a tool for writing emails, generating images, or powering...


Realme Neo7’s Massive 7000mAh Battery Revealed Ahead of Launch Realme is gearing up to unveil its latest mid-range smartphone, the Realme Neo7, in China on December...