Understanding Social Identity Authentication in Today’s Digital Landscape
Today’s digital world demands streamlined yet secure access to countless online services. Social identity authentication has emerged as a solution that promises both convenience and enhanced security. However, choosing the right approach requires careful consideration of trust factors, security features, and implementation strategies.
The fundamental question remains: should businesses and consumers embrace established social platforms as identity providers? The answer depends largely on understanding which platforms offer robust security measures and how to implement them effectively.
Evaluating Security Features Across Major Social Identity Providers
When assessing social identity authentication options, strong authentication capabilities become paramount. Leading platforms like Google, Microsoft, PayPal, and LinkedIn all offer multi-factor authentication through SMS-based one-time keys and device authorization controls.
Unfortunately, many users fail to activate these enhanced security features, often citing convenience concerns. This represents a significant vulnerability that organizations must address when implementing social identity authentication systems.
Consider the context of your authentication needs. Using PayPal credentials for financial transactions makes logical sense given their established trust in monetary dealings. Conversely, Twitter might be less appropriate for sensitive financial applications.
Trust Levels and Business Considerations
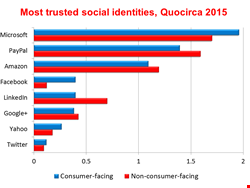
Research reveals fascinating insights about organizational trust in various social identity providers. Overall, social identities rank lowest in trustworthiness compared to government databases and telecommunications providers, with only 12% considering them highly trustworthy.
However, significant variations exist among different providers. Microsoft leads in business trust due to its established presence through Active Directory systems. Amazon and PayPal follow closely, benefiting from their proven track records in financial transactions.
Consumer-facing businesses show higher acceptance of Facebook authentication, while B2B organizations prefer LinkedIn. This variance highlights the importance of understanding your audience when selecting appropriate social identity authentication methods.
Implementation Strategies for Organizations
Successful deployment requires offering multiple authentication options rather than mandating specific platforms. Companies like Janrain, Gigya, and LoginRadius provide identity brokering solutions that handle this complexity automatically.
These platforms allow users to select their preferred social identity authentication method while maintaining seamless integration with your systems. Additionally, they often include fallback options for users who prefer traditional account creation.
Integrating Social Identity Authentication with Existing Systems
Modern organizations need comprehensive identity management strategies that encompass social identities alongside employee and partner credentials. This requires federated identity management capabilities that can handle diverse authentication sources under unified policies.
Single sign-on (SSO) systems play a crucial role in this integration. Many organizations are transitioning to cloud-based SSO solutions from providers like Ping Identity, Okta, and OneLogin to support their evolving authentication requirements.
The key lies in creating flexible access controls that can accommodate different user types while maintaining consistent security standards. For instance, travel booking systems might grant standard customers access to airline and hotel reservations while providing executive users additional concierge services.
Future-Proofing Your Authentication Strategy
As user bases expand and authentication requirements evolve, organizations must consider both on-premise and cloud-based identity solutions. Leading vendors now offer paired products that seamlessly bridge these environments.
This hybrid approach ensures scalability while maintaining security consistency across all authentication channels. Whether users authenticate through social platforms or traditional methods, the underlying security framework remains robust and unified.
Best Practices for Implementing Social Identity Authentication
Success in social identity authentication requires strategic planning and careful execution. Start by analyzing your user base to determine which social platforms they trust and actively use. This data should inform your platform selection process.
Next, ensure that your chosen platforms support strong authentication features and encourage users to enable them. Consider implementing educational campaigns that highlight the security benefits of multi-factor authentication.
Building trust takes time, but the convenience and security benefits of well-implemented social identity authentication make it worthwhile. As digital interactions continue expanding, organizations that master this balance will gain significant competitive advantages.
Remember that social identity authentication represents just one component of comprehensive identity management solutions. Success requires integrating these capabilities with existing security frameworks and maintaining flexibility for future authentication methods.
Furthermore, regular security audits and user education programs ensure that your social identity authentication implementation remains effective and secure over time. Consider partnering with specialized vendors who can provide ongoing support and security consulting services.

 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Infosecurity2 months ago
Infosecurity2 months ago
 Social Media2 months ago
Social Media2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Social Media2 months ago
Social Media2 months ago