How Dropped USB Sticks Became a Powerful Security Experiment and Awareness Lesson
Imagine walking across a university campus and spotting a USB stick on the ground. Would you pick it up? Would you plug it into your computer? A recent experiment at the University of Illinois suggests that most people would—and that’s exactly what makes dropped USB sticks such a potent security threat. The study, led by researcher Elie Bursztein and presented at the Black Hat Conference in Las Vegas, revealed startling results that every organization should heed.
The USB Drop Attack: A Simple Yet Effective Experiment
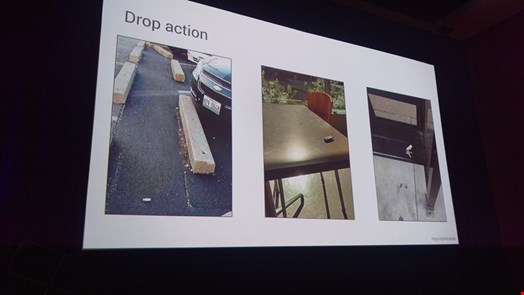
Bursztein and his team scattered 297 custom-built USB sticks across various locations on campus, including hallways, classrooms, parking lots, and academic buildings. The goal was straightforward: see how many people would pick them up and connect them to their devices.
Of the 297 sticks dropped, 290 were collected by passersby. Even more alarming, 135 of those—nearly 45%—were plugged into computers, triggering the intended payload. As Bursztein noted, the team essentially achieved “job done” the moment the USBs were dropped.
This isn’t just a theoretical exercise. The USB drop attack mimics real-world tactics used by malicious actors. Cybercriminals and even state-sponsored groups have employed similar methods to breach secure networks. The experiment underscores how easily human curiosity can be exploited.
Why Did People Plug in the USB Sticks?
To understand the psychology behind the behavior, the researchers included a survey file on each USB stick. Sixty-two people completed the survey, explaining their motivations. Many said they wanted to identify the owner and return the device. In fact, 53 individuals offered to return the USB key.
This reveals a critical insight: people often act with good intentions, but their actions can compromise security. The experiment shows that social engineering USB attack techniques rely on exploiting trust and helpfulness.
Building the Perfect Malicious USB Stick
Rather than using off-the-shelf tools like the USB Rubber Ducky, Bursztein built his own devices using a Teensy 32 development board. Each custom stick cost around $40 to produce. The team chose a social engineering attack vector over more complex methods like HID spoofing or zero-day exploits, partly because the university restricted the use of HTML5 payloads to avoid harming systems.
The USB sticks were programmed to work across Windows, macOS, and Linux. As Bursztein explained, spoofing isn’t new, but weaponizing it for multiple operating systems was a significant challenge. The final design ensured that once plugged in, the device would execute commands and “call home” to the attackers.
Which Locations Were Most Effective?
The experiment revealed that location matters. USB sticks dropped in parking lots had the highest pickup and plug-in rate, at 53%. Additionally, 68% of collectors admitted they opened files to determine the owner. Timing also played a role: 20% of the sticks were plugged in within the first hour, and 70% were activated within 35 hours.
To increase appeal, the team labeled some sticks with phrases like “confidential” or “final exam” and attached door keys to others. These tactics boosted curiosity and perceived value, making the USB security experiment even more successful.
Lessons for Businesses: Security Awareness Is Not Optional
The implications for organizations are clear. If university students and staff—who are generally tech-savvy—can be tricked so easily, corporate employees are equally vulnerable. The experiment serves as a stark reminder that USB security awareness training must be a priority.
Bursztein offered several recommendations to mitigate the risk. First, conduct regular awareness training that specifically addresses the danger of plugging in unknown devices. Second, encourage employees to be mindful of what they connect to their computers. As a last resort, consider blocking USB ports or using software like USBkill to restrict device access. However, Bursztein admitted that no solution is perfect.
For more on building a robust security culture, check out our guide on security awareness training best practices. Additionally, learn about preventing social engineering attacks in the workplace.
Conclusion: A Wake-Up Call for Cybersecurity
The University of Illinois experiment is more than an academic exercise—it’s a real-world demonstration of how easily security can be breached through simple human error. The success of these dropped USB sticks proves that technical defenses are only as strong as the people using them.
As Bursztein highlighted, the tactics behind such attacks require precision and detail, but the execution is surprisingly simple. Organizations must take this warning seriously and invest in comprehensive security awareness programs. After all, the next USB stick dropped in a parking lot might not be part of an experiment—it could be a real threat.
For a deeper dive into USB-based attacks, explore our article on USB attack vectors and how to protect your network.


 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Infosecurity2 months ago
Infosecurity2 months ago
 Social Media2 months ago
Social Media2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Social Media2 months ago
Social Media2 months ago