A Measured Victory in France’s Cyber War
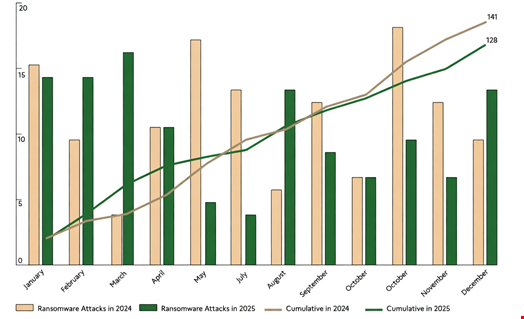
The numbers tell a story of cautious optimism. According to the French National Cybersecurity Agency (ANSSI), 2025 saw 128 reported ransomware attacks on French organizations. That’s a noticeable dip from the 141 incidents recorded the previous year.
This decline isn’t accidental. Vincent Strubel, ANSSI’s director general, and his team point directly to the impact of coordinated law enforcement actions and more effective defensive measures. It’s a sign that sustained pressure on cybercriminal networks can yield tangible results.
Who Was Hit and What Was Used?
While the overall trend is positive, the threat landscape remains complex and dangerous. Small and medium-sized businesses (SMBs) continued to bear the brunt of these attacks, representing the most frequent targets. However, the most significant year-over-year increases in targeting were seen in the healthcare and education sectors.
This shift suggests attackers are adapting their focus to where they perceive maximum pressure can be applied or where data is most sensitive. The tools of the trade also evolved. The Qilin ransomware strain was the most observed in 2025, accounting for 21% of incidents, followed by Akira (9%) and LockBit 3.0 (5%).
ANSSI also noted the emergence of over a dozen new strains, including Nova, Warlock, and Sinobi, appearing in at least one incident each. The criminal toolkit is never static.
The Impact of Global Law Enforcement
Why the drop? ANSSI’s analysis credits successful preventive work by cyber defenders and, crucially, large-scale international police operations. One operation stands out: Operation Endgame.
This coordinated action, involving multiple countries, is cited as having disrupted a significant portion of the ransomware infrastructure. More than just taking down servers, such operations sow distrust within the criminal ecosystem itself. When criminals can’t rely on their tools or their partners, their operations become riskier and less efficient.
A Broader Look at the Cyber Threat Landscape
Ransomware is just one piece of the puzzle. ANSSI’s annual report provides a wider lens on the cyber threats facing France. In 2025, the agency handled 3,586 cyber alerts requiring its support—an 18% decrease from 2024.
It’s important to contextualize that drop. 2024 was the year of the Paris Olympic and Paralympic Games, a period that naturally saw a heightened state of alert and a spike in reported signals. Of those thousands of alerts, ANSSI confirmed 1,366 as genuine cyber incidents involving a malicious actor, a number virtually identical to the 1,361 confirmed in 2024.
Two other trends stood out. The agency reported a significant increase in incidents related to data exfiltration claims. Yet they offer a critical warning: treat such claims with skepticism. Out of 460 events flagged as potential data leaks in 2025, only 42% were linked to actual, new compromises. The rest were false claims or the ‘recycling’ of old stolen data—a common intimidation tactic.
On a brighter note, ANSSI observed a substantial decrease in distributed denial-of-service (DDoS) attacks targeting French entities in 2025.
The Blurring Lines of Cyber Conflict
Perhaps the most concerning long-term trend identified in the report is the growing ‘fog’ of cyber operations. The lines between nation-state actors and cybercriminals are becoming deliberately blurred.
Groups from both spheres are increasingly sharing capabilities, tools, and techniques. They adopt each other’s practices, creating a murky environment where attribution—figuring out exactly who is behind an attack—becomes immensely difficult. This ‘division of labor’ among specialized actors makes attacks more sophisticated and resilient.
Strubel pointed to the series of cyber-attacks against Polish electrical infrastructure at the end of 2025 as a stark warning. It “raises the specter of the feared scenario for which France is preparing,” he stated. The scenario? By 2030, France could face a massive increase in hybrid attacks where cyber operations have concrete, potentially destructive effects on critical national infrastructure.
His final message, however, was one of resolve. “Yes, France has the means to counter, deter, or at least significantly complicate the work of attackers.” The 2025 ransomware dip is a battle won, but the cyber war is a long-term campaign.


 CyberSecurity2 days ago
CyberSecurity2 days ago
 CyberSecurity2 days ago
CyberSecurity2 days ago
 Infosecurity21 hours ago
Infosecurity21 hours ago
 CyberSecurity2 days ago
CyberSecurity2 days ago
 CyberSecurity2 days ago
CyberSecurity2 days ago
 CyberSecurity2 days ago
CyberSecurity2 days ago
 CyberSecurity2 days ago
CyberSecurity2 days ago
 CyberSecurity2 days ago
CyberSecurity2 days ago