

How Humans and Machines Can Unite to Fight Phishing Attacks When organizations aim to fight phishing, they often turn first to technology. Firewalls, spam filters, and...


How MSSPs Are Solving the Cybersecurity Workforce Crisis in Healthcare The cybersecurity workforce shortage has become a defining challenge for industries worldwide, but healthcare faces an...


Microsoft Patches Two Zero-Day Vulnerabilities in April Patch Tuesday Release Microsoft has rolled out its April Patch Tuesday update, addressing a significant number of security flaws,...
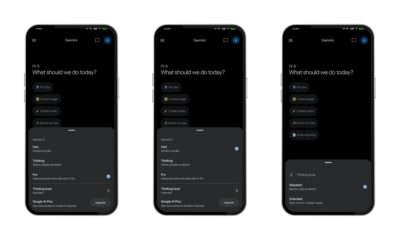

Google Gemini’s New ‘Thinking Level’ Lets You Dial Up the Brainpower — Here’s How It Works With Google I/O 2026 just around the corner, fresh leaks...


Alleged Chinese State-Sponsored Hacker Extradited to the United States After Italian Arrest A man suspected of orchestrating cyberattacks on behalf of Beijing has been extradited to...


YoCutie App Review: 100% Free Dating for All Android Devices Looking for a free dating app that actually works without hidden fees? YoCutie might be the...


The Hidden Danger of AI: How Instant Answers Could Make Us Think Less Artificial intelligence has transformed how we access information. With a simple query, chatbots...


Imagine waking up one day to discover that your government has handed every citizen a premium subscription to ChatGPT Plus. That is exactly what is happening...


New EU Regulations: What GDPR Means for Data Breach Notification Obligations The countdown is on. With less than nine months until the enforcement date, organizations across...


How to Make a WhatsApp Sticker from Your Photo: The Ultimate Guide for Custom Chat Fun Have you ever wanted to turn your favourite selfie into...