

How Google Workspace with Gemini Acts as an AI Co-Founder for Small Business Scaling Every small business starts with a spark: a big idea, a tiny...


Samsung One UI 7 Beta Released: A Deep Dive Into the Exciting New Features Samsung has officially launched the Samsung One UI 7 beta, giving Galaxy...


Grok Voice Mode Arrives on CarPlay: A Sarcastic AI Copilot for Your Commute Imagine pulling into traffic and having an AI with a sharp tongue and...


Why API Dependancy, IoT Expansion, and GDPR Will Define Cybersecurity in 2017, According to (ISC)2 As the digital economy accelerates, 2017 is poised to be a...


How to Check UP Board High School & Intermediate Exam Results 2025: A Complete Guide Every year, millions of students across Uttar Pradesh eagerly await their...


Operation Atlantic Freezes $12 Million in Crypto Losses: How Approval Phishing Scams Were Disrupted In a coordinated crackdown spanning three continents, law enforcement agencies from the...
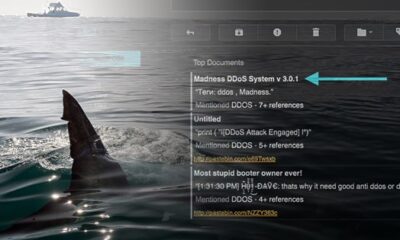

Exploit Threats Evolve: The Emergence of TrickLoader and TrickBot Cybersecurity experts have identified a troubling shift in the exploit landscape. The market for malicious tools is...


How to Manage the Growing Influx of VDI and Desktop-as-a-Service in Modern Enterprises Over the past two decades, the corporate world has undergone a dramatic transformation....


Transform Your Phone with Diamond Wallpaper HD for Android: A Step-by-Step Guide Are you tired of the same old, boring wallpaper on your Android device? Many...


OpenAI Codex Chrome Extension: AI Agent Moves Into Your Browser for Real Work OpenAI has taken a significant step forward with its OpenAI Codex Chrome extension,...