CyberSecurity
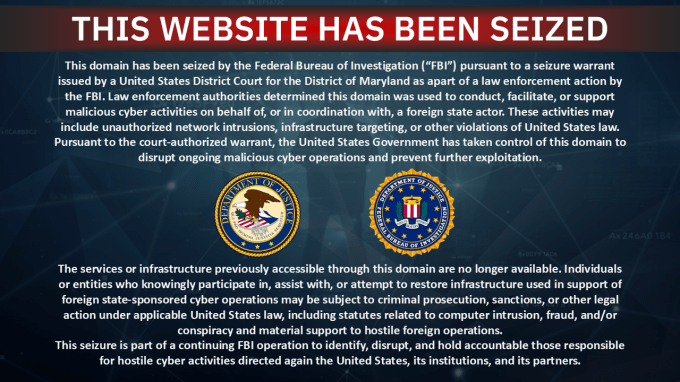
FBI Seizes Pro-Iranian Hacker Group Handala’s Websites Following Stryker Attack
CyberSecurity
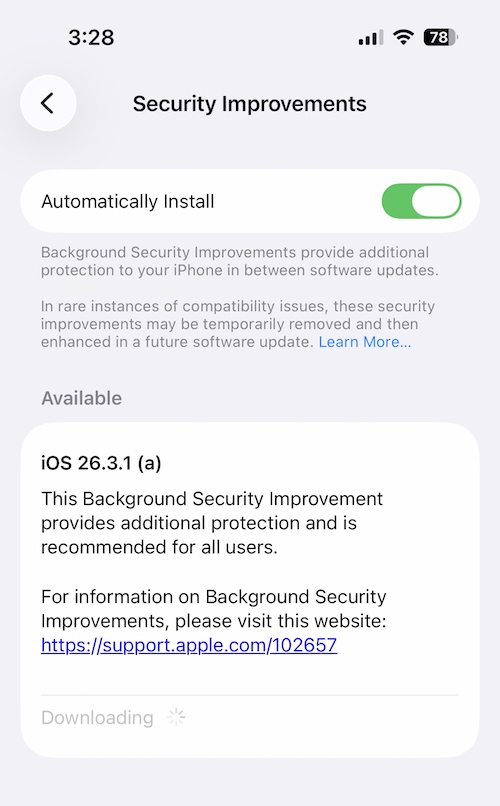
Apple’s First Background Security Update Fixes Critical Safari Bug
CyberSecurity
LeakyLooker: How Google Looker Vulnerabilities Risked Cloud Data
CyberSecurity
Russian Hackers Target WhatsApp and Signal in Global Espionage Campaign
-

 CyberSecurity2 weeks ago
CyberSecurity2 weeks agoZero-Day Attacks Hit Record High as Enterprise Software Becomes Prime Target
-

 Infosecurity1 week ago
Infosecurity1 week agoCybersecurity Communication: Why Fear-Based Messaging Fails and What Works
-

 CyberSecurity2 weeks ago
CyberSecurity2 weeks agoLeakBase Data Breach Forum Seized in Major Europol Operation
-

 CyberSecurity2 weeks ago
CyberSecurity2 weeks agoCyber 150 Awards Reveal AI Security Startups Are Leading Industry Growth
-

 CyberSecurity2 weeks ago
CyberSecurity2 weeks agoContextCrush Vulnerability: How a Trusted AI Tool Became an Attack Vector
-

 CyberSecurity1 week ago
CyberSecurity1 week agoInfosecurity Europe 2026 Keynote Speakers: Cybersecurity Leaders, Elite Athletes & Special Forces
-

 Infosecurity1 week ago
Infosecurity1 week agoCyber Warfare and Critical Infrastructure: The Hidden Threat in Foreign-Built Systems
-

 Infosecurity1 week ago
Infosecurity1 week agoCybersecurity Investment Soars as VCs Bet on Business Solutions