

Discover The Best Stranger Online Chat App of All Times! Are you looking for a way to meet new people and have fun conversations without revealing...


How to Hire and Get Hired in Information Security: Expert Advice from (ISC)2 Congress Imagine walking into a conference session, only to realize within minutes that...


How to Build Up Infosec Professionals Through Mentoring: Expert Insights from RSA’s Jeff Silver In the fast-paced world of information security, finding and keeping top talent...

How Gemini Is Reshaping the In-Car Experience: A New Era of Smart Driving For years, talking to your car has felt like a one-sided conversation. You...


Growing a YouTube channel from scratch can feel like shouting into a void. You upload, you wait, and often, nothing happens. Yet some creators manage to...


Silent Security Risk: Google API Keys Quietly Grant Gemini Access on Android A newly uncovered flaw in Google’s API key system is putting Android applications at...


Why Tenacity and Problem-Solving Matter More Than a CISSP in Cybersecurity At the CLOUDSEC conference in London back in September 2016, Trend Micro’s vice president of...
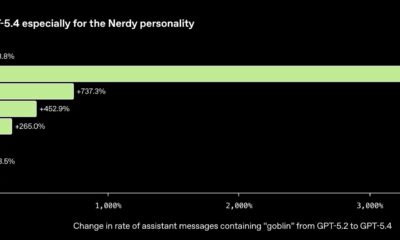

ChatGPT Is Finally Done Talking About Goblins and Gremlins After OpenAI Ditches Its “Nerdy” Persona If you’ve recently asked ChatGPT for help with a recipe or...


If you own a Samsung Galaxy smartphone, you’re likely familiar with its robust feature set. However, many users overlook a powerful hidden feature that can significantly...


Adobe patches PDF zero-day vulnerability exploited for months by hackers Adobe has released an urgent security update for its widely-used PDF software, Acrobat and Reader, to...