

Google finally explains why Android AICore keeps eating your storage — and it actually makes a lot of sense If you’ve ever glanced at your Android...


Page Not Found: What to Do When You Hit a 404 Error on Infosecurity Magazine Did you just land on a Page Not Found message while...
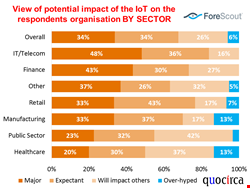

IoT Deployments Often Rely on Isolated Networks and Sub-Nets: How to Secure the Expanding Attack Surface The Internet of Things (IoT) promises to revolutionise business processes,...

If you own a Samsung Galaxy S26 Ultra, you’re likely already aware that its built-in S-Pen is more than just a fancy stylus. However, what many...


In the vast ocean of YouTube content, where millions of creators compete for attention, there exists a hidden YouTube niche that quietly amasses a staggering 1...
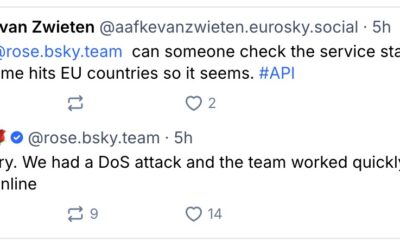

Bluesky Experiences Service Disruption: What Users Need to Know If you’ve been struggling to access Bluesky today, you’re not alone. The social network is currently grappling...


WhatsApp Emoji Reactions: A New Way to Express Yourself in Chats Have you ever wished you could quickly respond to a friend’s message on WhatsApp without...


How to Avoid Joining WhatsApp Groups: Essential Tips for Privacy Control Are you tired of being added to random WhatsApp groups without your consent? You are...
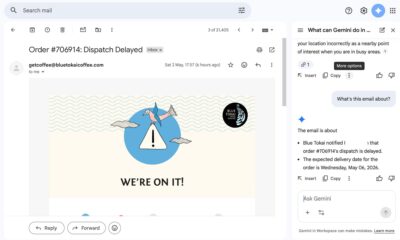

I Let Gemini Take Over My Gmail—Here’s What Happened My inbox used to feel like a black hole. Between meeting invites, marketing pitches, product PR, and...


Why Organizations Should Aim for a Risk-Adverse Culture, Not Just Compliance For many organizations, security training boils down to a checkbox exercise: prove that every employee...