How to Manage the Growing Influx of VDI and Desktop-as-a-Service in Modern Enterprises
Over the past two decades, the corporate world has undergone a dramatic transformation. Gone are the days of sprawling server rooms and bulky desktop computers tethered to landlines. The rise of cloud computing, remote workforces, and the Internet of Things (IoT) has reshaped how businesses operate. At the heart of this shift lies the increasing adoption of VDI and Desktop-as-a-Service—two technologies that are redefining how employees access their workspaces. But as these solutions proliferate, many organizations struggle to manage the influx effectively. This article explores practical strategies for handling this transition while maintaining security, controlling costs, and ensuring productivity.
Understanding the Shift: From Local Desktops to Virtual Workspaces
Traditionally, employees relied on locally installed operating systems and applications on their desktop or laptop computers. Data was stored on the device itself, making management straightforward but risky. If one machine became compromised, the entire enterprise network could be at risk. The emergence of cloud technology and remote work changed everything. Employees began taking devices home, complicating policy enforcement and security updates. This is where thin clients entered the picture. These lightweight devices with minimal local resources connect to centralized servers, reducing costs and improving control. However, the real game-changer came with virtual desktop infrastructure (VDI) and desktop-as-a-service (DaaS), which allow users to access a full desktop environment from anywhere, on any device.
Building on this, businesses now face a critical choice: adopt VDI or DaaS? Each model offers distinct advantages, but managing their influx requires a clear understanding of their differences and implications.
VDI vs. DaaS: Choosing the Right Model for Your Organization
VDI involves a company’s own servers delivering desktops to employee devices. The business retains full control over infrastructure, maintenance, and security updates. This is ideal for organizations with dedicated IT teams and strict compliance requirements. In contrast, DaaS is fully outsourced—employees simply connect to the internet and a cloud service, while the hosting provider handles all backend management. Think of VDI as half-board accommodation and DaaS as an all-inclusive resort. Both are excellent options, but they demand different approaches to management.
As a result, many businesses wonder: which is more secure? The answer depends on your context. DaaS providers often have robust security protocols, but trusting an external organization with sensitive data can be daunting. That said, DaaS is generally better suited for BYOD (bring your own device) policies, as all devices are managed behind the virtual desktop service, reducing the attack surface. On the other hand, VDI offers greater control for industries like healthcare or finance, where data sovereignty is paramount.
Key Strategies for Managing the Influx of Virtual Desktops
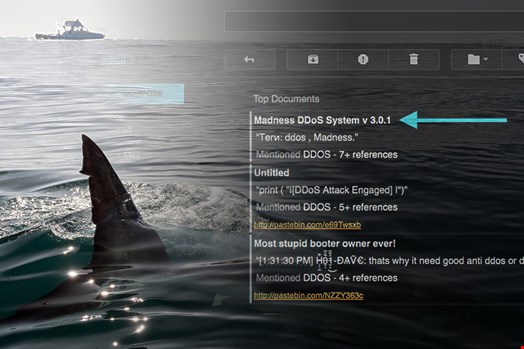
1. Prioritize Security from Day One
Security concerns often top the list when adopting VDI and Desktop-as-a-Service. To manage the influx effectively, start by assessing your organization’s risk profile. For DaaS, ensure your provider complies with industry standards like GDPR or HIPAA. For VDI, implement multi-factor authentication and regular patch management. Remember, the goal is to minimize the number of systems storing sensitive data—virtual desktops can help achieve that by centralizing resources.
2. Control Costs with Transparent Licensing
Cost is a major driver for adopting DaaS, especially for SMBs and healthcare organizations. However, hidden expenses can arise if you don’t understand your licensing agreement. For instance, if your company acquires another firm, DaaS costs may increase per user. Always clarify pricing breaks and scalability options upfront. With VDI, factor in hardware and maintenance costs. A clear cost analysis will help you manage the influx without budget surprises.
3. Streamline Deployment with Automation
Managing a large number of virtual desktops manually is inefficient. Use automation tools to provision, update, and decommission desktops quickly. This reduces IT workload and ensures consistent configurations across the organization. For example, integrating with cloud management platforms can simplify scaling during peak demand.
4. Train Employees for a Seamless Transition
User adoption is often overlooked. Provide training on how to access and use virtual desktops, especially for remote workers. Clear communication about security practices, like using strong passwords and avoiding public Wi-Fi, can prevent issues. When employees feel comfortable, the influx becomes an opportunity rather than a burden.
Real-World Applications: SMBs and Healthcare Lead the Way
Small and medium-sized businesses (SMBs) are among the biggest beneficiaries of VDI and Desktop-as-a-Service. They enjoy lower operational costs and reduced IT overhead, allowing them to focus on growth. Healthcare organizations, meanwhile, leverage the security benefits to protect patient data. For instance, a hospital using DaaS can ensure that sensitive information never leaves the virtual environment, even when doctors use personal devices. These sectors demonstrate how strategic management of virtual desktop influx can drive efficiency and compliance.
Conclusion: Embrace Change with a Clear Plan
The enterprise landscape will continue to evolve as resources become more virtualized. VDI and DaaS are not fleeting trends; they represent fundamental shifts in how work gets done. By prioritizing security, controlling costs, automating deployment, and training users, organizations can manage the influx smoothly. Whether you choose VDI’s control or DaaS’s convenience, the key is to align your strategy with business goals. For more insights, explore our guide on virtual desktop security best practices or learn about cloud migration strategies. Start planning today to turn this technological wave into a competitive advantage.
For further reading, check out Infosecurity Magazine for expert analysis on cybersecurity trends.


 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Infosecurity2 months ago
Infosecurity2 months ago
 Social Media2 months ago
Social Media2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Social Media2 months ago
Social Media2 months ago