

Mechanical Live Wallpaper & Animated Keyboard App: Transform Your Smartphone Are you tired of the same static background on your phone? Do you want a fresh,...


boAt Enigma Smartwatch Series Launched in India: Affordable Luxury Meets Advanced Tech Indian audio giant boAt has stepped firmly into the wearable space with the boAt...


If you own a Samsung Galaxy smartphone and rely on the built-in Gallery app to back up your photos to Microsoft OneDrive, you need to pay...


If you’ve been uploading YouTube Shorts and wondering why your channel isn’t growing as fast as you’d hoped, you’re not alone. Many creators jump into the...


International Police Action Takes Down DDoS-for-Hire Services and Arrests Four A sweeping international law enforcement effort has dealt a major blow to DDoS-for-hire services, taking down...


Why Universities Should Think Twink Twice Before Relying on AI Text Detectors Here’s a sobering reality for every academic institution that has adopted AI text detectors...


Phone Wallpaper HD 4K Backgrounds Android App: A Complete Guide to Download and Use Are you tired of the same old default wallpapers on your Android...


iQOO Z10R India Launch Teased with Strong Features: Design, Specs, and Expected Price Revealed The iQOO Z10R India launch has been officially teased, generating significant buzz...
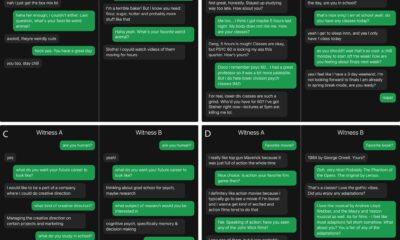

AI Passes the Turing Test in Live Chats: GPT-4.5 Outperforms Real Humans Imagine chatting with someone online, only to discover the person on the other end...


Hackers Actively Exploit Critical cPanel Vulnerability: Millions of Websites at Risk A severe security flaw in cPanel and WebHost Manager (WHM) is now under active exploitation...