Bluesky Confirms Sophisticated DDoS Attack Behind Persistent App and Website Outages
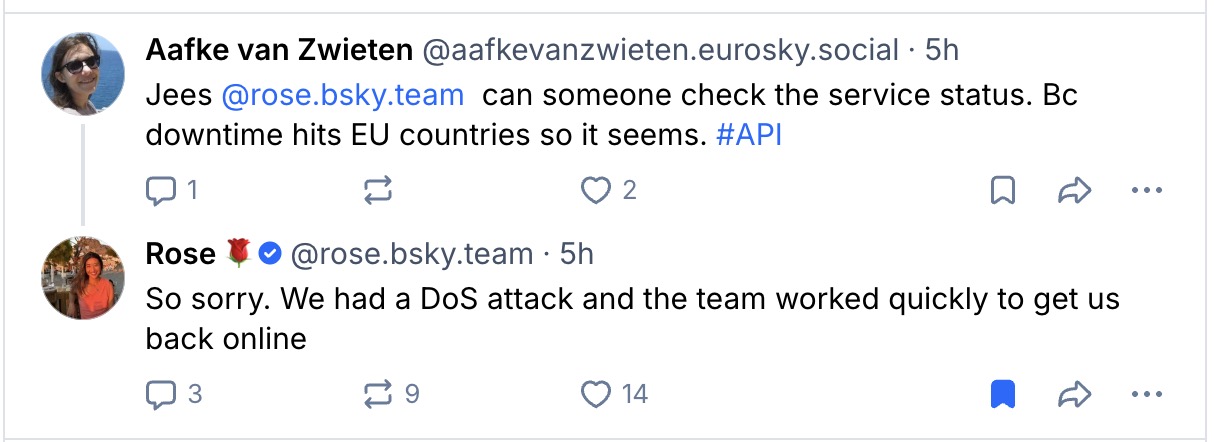
Bluesky, the decentralized social network, has publicly confirmed that a sophisticated Bluesky DDoS attack is the root cause of the ongoing service interruptions that have plagued its platform since mid-April. Chief operating officer Rose Wang initially attributed the problems to a cyberattack, and the company later clarified that a Distributed Denial-of-Service (DDoS) assault began on April 15 at around 8:40 p.m. ET. This revelation has left many users frustrated as intermittent outages continue to disrupt feeds, notifications, and search functions.
As of Friday, the platform is still struggling to fully restore normal operations. The company posted on its official Bluesky account that the attack is “impacting our operations, with users experiencing intermittent interruptions in service for their feeds, notifications, threads, and search.” However, Bluesky has assured users that there is no evidence of unauthorized access to private data. For those seeking updates, the status.bsky.app page has been unreliable, often failing to load itself.
What Is a DDoS Attack and How Does It Affect Bluesky?
A Distributed Denial-of-Service (DDoS) attack involves flooding an app or website with massive amounts of junk traffic, effectively overloading servers and knocking them offline. This type of cyberattack does not involve breaching internal systems or stealing data, but it can be highly disruptive. In Bluesky’s case, the attack has caused the site and app to load slowly at times or display error messages like “This feed is currently receiving high traffic and is temporarily unavailable. Please try again later. Message from server: Rate Limit Exceeded.”
Popular feeds such as Discover and the official Bluesky Team feed are particularly affected, even when users’ personal feeds remain functional. Additionally, attempting to view a user’s profile often results in an error, forcing repeated refreshes. Bluesky protocol engineer Bryan Newbold noted the severity early on, posting around 3:46 a.m. ET on Wednesday, “oof, our services are getting hit pretty hard tonight.”
Impact on Users and the Broader Decentralized Ecosystem
The Bluesky outage has not only frustrated regular users but also sparked a notable shift within the decentralized social network ecosystem. Communities like Blacksky, which run their own infrastructure on the underlying AT Protocol, have remained functional. Blacksky’s team reported a “significant spike” in migration requests from Bluesky users over the past 12 hours, as alternatives like Eurosky and other ATmosphere founders promoted their services. This demonstrates how a major Bluesky DDoS attack can accelerate user movement within the decentralized web.
For many users, the intermittent nature of the outages adds to the frustration. One moment the app loads, albeit slowly; the next, it displays error messages. The company has not provided a definitive timeline for a fix, though it promised an update by 1 p.m. ET on Friday. Meanwhile, the status page itself has been unreliable, with a typo visible in one message: “investigating an incident with service in one of our reginos [sic].” This suggests the team is operating under significant pressure.
Bluesky’s Response and Mitigation Efforts
Bluesky’s team worked through the night to mitigate the attack, but it intensified throughout the day. The company has been transparent about the cause, but the lack of a rapid resolution has tested user patience. As of now, the best advice for users is to check Bluesky’s status page for updates, though it may not always be accessible. For those considering alternatives, the decentralized nature of the AT Protocol means other services like Blacksky remain operational, offering a temporary refuge.
This incident highlights the vulnerabilities even in modern, decentralized platforms. While DDoS attacks are not new, their sophistication continues to evolve. Bluesky’s experience serves as a reminder of the importance of robust cybersecurity measures and backup infrastructure. For more on how social media platforms handle cyber threats, read our guide on securing your social media accounts.
What’s Next for Bluesky?
Building on the current situation, Bluesky must prioritize restoring full service and preventing future attacks. The company has not indicated whether it will implement additional protections, but the incident underscores the need for scalable defenses. As users explore alternatives, Bluesky’s ability to recover quickly will be crucial for retaining its community. The decentralized social network model offers resilience, but as this Bluesky DDoS attack shows, no platform is immune to disruption.
In the meantime, affected users can follow alternative decentralized platforms that are still functioning. The team at Bluesky continues to work on mitigation, and we will update this story as more information becomes available.

 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Infosecurity2 months ago
Infosecurity2 months ago
 Social Media2 months ago
Social Media2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Social Media2 months ago
Social Media2 months ago








