Operation Alice: How Police Took Down 370,000+ Dark Web Sites
Imagine a criminal marketplace so vast it spans hundreds of thousands of hidden websites. Now picture that entire network being a police trap. That’s exactly what happened in a recent international sting operation that crippled a major dark web fraud scheme.
The Five-Year Honeypot Operation
For nearly five years, a platform called “Alice with Violence CP” operated on the dark web. It advertised child sexual abuse material (CSAM) and cybercrime-as-a-service offerings like stolen credit card data. Thousands of customers worldwide flocked to it, paying in Bitcoin for illegal content.
There was just one problem: none of it was real. The entire operation was a sophisticated scam designed to swindle criminals out of their money. What the customers didn’t know was that law enforcement had been watching the entire time.
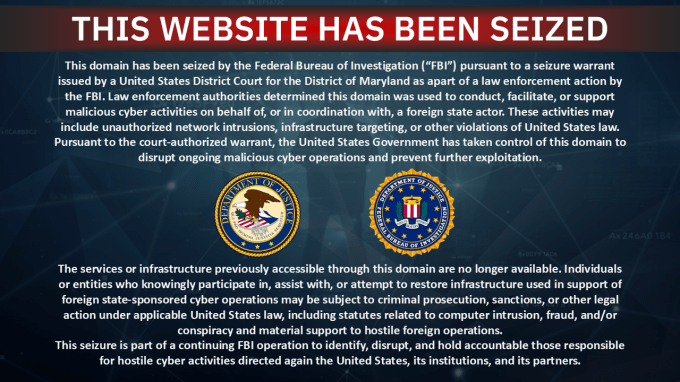
German authorities, leading what they called Operation Alice, turned this criminal enterprise into one of the largest honeypots in cyber policing history. From March 9-19, they finally pulled the trigger, dismantling the entire network.
Unmasking the Criminal Customers
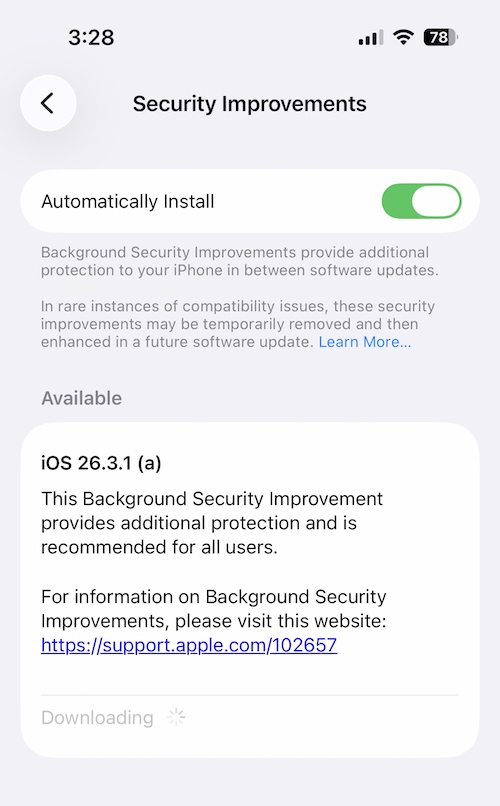
While the sites were fake, the criminal intent of the customers was very real. This presented a unique opportunity for investigators. As would-be buyers provided email addresses and made Bitcoin payments for non-existent content, they were essentially handing police their digital fingerprints.
International cooperation through Europol allowed authorities to identify 440 individuals who attempted to purchase illegal material. Over 100 of these cases are now under active investigation. When children were believed to be in immediate danger, police moved swiftly.
In one August 2023 case, Bavarian police searched the home of a 31-year-old father who tried to buy €20 worth of CSAM. He was subsequently convicted. These targeted interventions demonstrate how digital investigations translate into real-world protection.
The Mastermind Behind the Fraud
Police traced the operation to a 35-year-old Chinese national who had been running the scheme since 2019. His technical setup was staggering: over 373,000 .onion sites distributed across 287 servers, with 105 of those servers located in Germany alone.
Between February 2020 and July 2025, he advertised his fake wares through more than 90,000 different onion domains. Customers could purchase “packages” ranging from €17 to €215, supposedly containing anywhere from a few gigabytes to several terabytes of illegal material.
The profits were substantial. Investigators estimate he made over €345,000 from approximately 10,000 duped customers worldwide. An international arrest warrant has now been issued for his capture.
Global Law Enforcement Collaboration
Operation Alice wasn’t a solo effort. Twenty-two countries participated in the takedown, including the United States, United Kingdom, Ukraine, Switzerland, Sweden, Spain, Italy, France, Canada, Australia, and Belgium. This level of international coordination is becoming increasingly crucial in fighting borderless cybercrime.
The success follows another major victory against dark web CSAM platforms. Last year’s Operation Stream, also led by Bavarian authorities with Europol support, took down the Kidflix platform. That operation identified 1,393 suspects worldwide from over 1.8 million registered users.
Unlike Alice with Violence CP, Kidflix actually distributed real child abuse material. The contrast between these two operations shows law enforcement’s evolving strategies: sometimes they dismantle genuine criminal platforms, other times they turn fraudulent ones into intelligence-gathering tools.
What does this mean for the future of dark web policing? The message is clear: even in the most hidden corners of the internet, criminal activity leaves traces. And international law enforcement is getting better at following those traces back to their source.


 CyberSecurity2 weeks ago
CyberSecurity2 weeks ago
 CyberSecurity2 weeks ago
CyberSecurity2 weeks ago
 Infosecurity2 weeks ago
Infosecurity2 weeks ago
 CyberSecurity2 weeks ago
CyberSecurity2 weeks ago
 CyberSecurity2 weeks ago
CyberSecurity2 weeks ago
 CyberSecurity2 weeks ago
CyberSecurity2 weeks ago
 Infosecurity2 weeks ago
Infosecurity2 weeks ago
 Infosecurity2 weeks ago
Infosecurity2 weeks ago