
NIST Drops NVD Enrichment for Pre-March 2026 Vulnerabilities: What It Means for Cybersecurity The NVD enrichment process is undergoing a major overhaul. The US National Institute...

Cookeville Regional Medical Center Discloses Rhysida Ransomware Attack Affecting 337,917 Patients A major Rhysida ransomware breach has hit Cookeville Regional Medical Center (CRMC) in Tennessee, exposing...


APK Malformation: How Attackers Are Bypassing Android Security Checks When it comes to APK malformation, the numbers are staggering. Researchers from Cleafy’s Threat Intelligence and Incident...


Two US Nationals Sentenced for Running Fake IT Worker Network for North Korea A federal court in New Jersey has handed down prison sentences to two...


Microsoft Patches Two Zero-Day Vulnerabilities in April Patch Tuesday Release Microsoft has rolled out its April Patch Tuesday update, addressing a significant number of security flaws,...


Sharp Rise in Brute-Force Attacks Targets SonicWall and Fortinet Devices, Researchers Warn Security researchers have observed a dramatic increase in brute-force attacks aimed at compromising SonicWall...


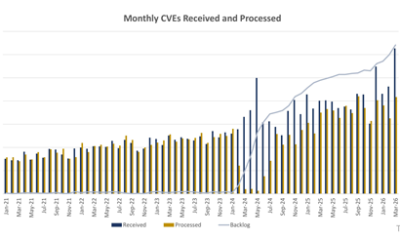
AI Companies Like OpenAI and Anthropic to Play Bigger Role in CVE Program, Says CISA The world’s largest vulnerability disclosure scheme is opening its doors wider...


Critical Nginx-ui MCP Flaw Actively Exploited in the Wild A critical nginx-ui MCP flaw is being actively exploited, putting thousands of servers at risk. Tracked as...


How a Signed Adware Operation Silently Disabled Antivirus on 23,000 Hosts Worldwide A new signed adware operation linked to Dragon Boss Solutions LLC has been quietly...


ENISA Aims for Top-Tier Role in CVE Program: What It Means for EU Cybersecurity The European Union Agency for Cybersecurity (ENISA) is pushing for a more...