The Cybersecurity Gap: Why Awareness Isn’t Enough to Stop Human Error
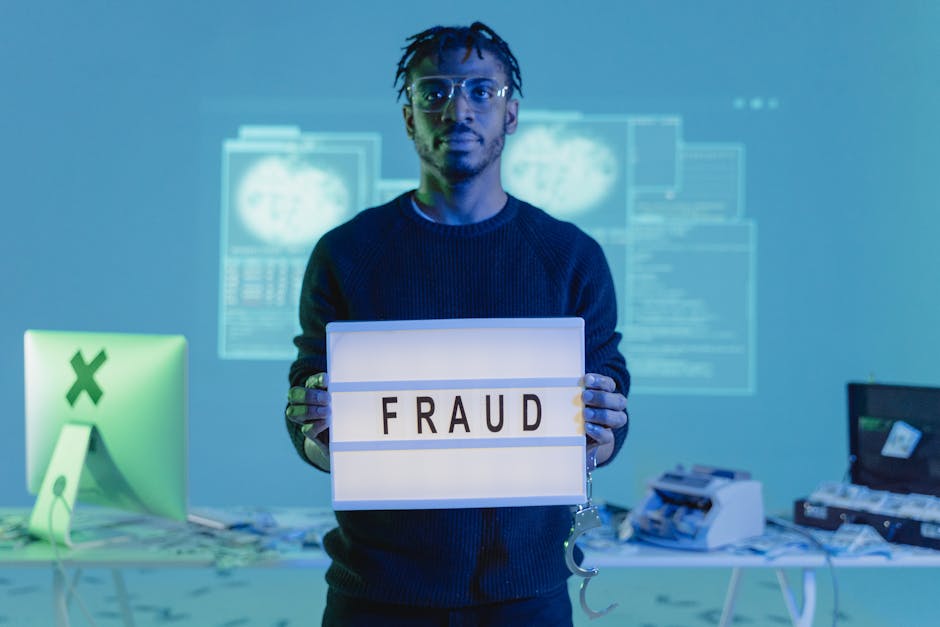
Organizations worldwide pour billions into firewalls, encryption, and advanced threat detection. Yet, a persistent vulnerability remains untouched by technology alone: the human element. This human factor cybersecurity challenge represents the critical disconnect between what people know about threats and how they actually behave online.
Building on this, recent high-profile breaches continue to spotlight a troubling reality. Technical defenses can be bypassed through simple human mistakes—a clicked link, a weak password, a misplaced file. Consequently, security leaders face a fundamental question: how do we transform awareness into lasting behavioral change?
The Awareness-Behavior Paradox in Security
Public consciousness about cyber threats has undoubtedly grown. Media coverage of major incidents, like the TalkTalk breach, sparked widespread conversation. People now recognize terms like “phishing” and “data breach.” However, recognition does not equal protection.
This means that despite increased awareness, fundamental security practices remain neglected. For years, lists of the worst passwords, compiled by firms like SplashData, have featured predictable choices like “123456” and “password.” Their continued dominance suggests a failure to translate general concern into specific, secure actions.
Where Technical Solutions Fall Short
Dr. Jessica Barker, a consultant specializing in the psychology of security, observes this gap firsthand. “In the last year there’s been a big rise in awareness,” she notes, “but behaviors haven’t really changed.” The industry’s instinct is to seek a technical fix—more software, newer hardware. Yet, the most reliable attack vector remains a person.
Therefore, strategies focused purely on technology miss the mark. A sophisticated spear-phishing campaign, for instance, often targets human curiosity or authority, not system vulnerabilities. An employee clicking one malicious link can neutralize millions in security investment.
Education: The Critical Bridge to Secure Behavior
So, what’s the solution? The consensus points decisively toward education and empowerment. Dr. Adrian Davis, Managing Director EMEA at (ISC)², argues that investing in staff literacy is as valuable as buying technology. “You can buy lots of security technology,” he warns, “but if you don’t have the staff to understand the value of that technology, then it could turn out to be a waste of money.”
In addition, effective training must move beyond technical jargon. Bombarding employees with complex terminology creates confusion, not competence. The goal is to convey the “why” behind security policies in relatable terms, helping staff visualize the consequences of their actions.
From Myth to Method: Applying Behavioral Science
Dr. Barker’s research delves into how messaging influences outcomes. She references the “Pygmalion effect,” a psychological phenomenon where high expectations lead to improved performance. In a security context, this theory is powerful. Treating employees as the weakest link often creates exactly that outcome.
Conversely, when organizations frame staff as essential defenders and equip them with clear, actionable knowledge, behavior shifts. Empowering someone to confidently report a suspicious email is more effective than simply telling them “don’t click links.”
The Simple Tools We Ignore
A striking example of the awareness-behavior gap is two-factor authentication (2FA). It’s one of the most effective safeguards available. Yet, Dr. Barker’s survey found 80% of people didn’t know what it was, and 70% weren’t using it. This highlights a massive opportunity: implementing and explaining foundational tools.
As a result, security programs must prioritize usability. If a security measure is perceived as too cumbersome, people will find workarounds, creating new risks. The ideal human factor cybersecurity strategy makes the secure path the easiest one.
Building a Human-Centric Security Culture
Ultimately, mitigating the insider threat requires a cultural shift. The UK’s Information Commissioner’s Office (ICO) finds that most breaches it investigates stem from human error that training could have prevented. This isn’t about blaming individuals but about building resilient systems and mindsets.
On the other hand, creating this culture demands consistent effort. It involves regular, engaging training that evolves with the threat landscape, leadership that models secure behavior, and an environment where reporting potential threats is encouraged, not punished. For more on building this culture, see our guide on creating a security-first workplace.
In conclusion, the battle for cybersecurity will be won or lost in the human mind. Technology provides essential tools, but people determine how they’re used. By closing the gap between awareness and action—by focusing on the human factor cybersecurity—organizations can transform their greatest vulnerability into their strongest defense.

 CyberSecurity1 month ago
CyberSecurity1 month ago
 CyberSecurity1 month ago
CyberSecurity1 month ago
 Infosecurity4 weeks ago
Infosecurity4 weeks ago
 CyberSecurity4 weeks ago
CyberSecurity4 weeks ago
 CyberSecurity1 month ago
CyberSecurity1 month ago
 CyberSecurity1 month ago
CyberSecurity1 month ago
 How To3 weeks ago
How To3 weeks ago
 How To2 weeks ago
How To2 weeks ago