The Rise of the Threat Hunter: Proactive Cyber Defense for Modern Businesses
Cyberattacks are no longer a question of if, but when. For many organizations, the first sign of a breach comes from an external source—a customer, a partner, or even law enforcement. This reactive stance is costly, both financially and reputationally. As a result, a growing number of businesses are turning to a specialized role: the threat hunter. This professional doesn’t just wait for alarms to sound; they actively seek out vulnerabilities before attackers can exploit them. In this article, we explore how to identify and integrate a threat hunter into your cyber defense strategy.
Why Traditional Incident Response Falls Short
Most security teams focus on prevention and incident response—building walls and cleaning up after a break-in. However, this approach leaves a critical gap. According to recent data, over two-thirds of large UK businesses experienced a cyberattack in the past year, yet many only discovered the breach through a third party. This delay in detection can mean weeks or months of undetected activity, during which sensitive data is exfiltrated and systems are compromised.
Building on this, the costs of a delayed response are staggering. Beyond immediate financial losses, companies face regulatory fines, legal fees, and long-term brand damage. Therefore, a purely reactive strategy is no longer sufficient. Organizations must shift toward proactive detection and rapid containment.
What Is a Threat Hunter and How Do They Operate?
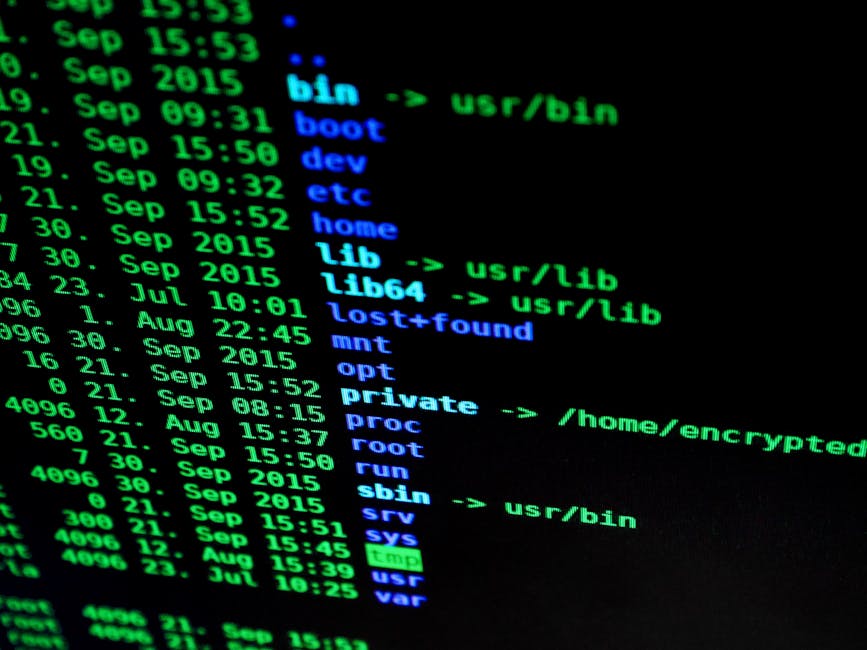
A threat hunter is a cybersecurity specialist who adopts an attacker’s mindset to uncover hidden threats. Unlike traditional security analysts who rely on automated alerts, threat hunters manually probe networks, systems, and applications for signs of compromise. They look for anomalies—unusual network traffic, unexpected file changes, or suspicious user behavior—that might indicate a breach in progress.
Think of them as an internal penetration tester, but with a continuous, ongoing mission. Instead of a one-time audit, they provide persistent vigilance. This proactive approach helps organizations identify weaknesses before cybercriminals can act. As a result, businesses can reduce the dwell time of attackers, minimizing damage and recovery costs.
Key Skills Every Threat Hunter Must Have
To be effective, a threat hunter needs a broad and deep technical skill set. They should understand network architecture, operating systems, application security, and common attack vectors. But technical know-how alone isn’t enough. The best threat hunters possess strong analytical thinking and curiosity—they ask “what if” and follow trails that others might ignore.
Furthermore, they must be adept with tools like SIEM platforms, endpoint detection and response (EDR) systems, and threat intelligence feeds. However, the human element remains crucial. Machines can flag anomalies, but only a skilled analyst can interpret context and prioritize threats.
How to Identify the Right Threat Hunter for Your Team
Finding a qualified threat hunter can be challenging, especially for small and medium-sized businesses (SMBs) with limited budgets. The ideal candidate has hands-on experience across multiple domains: network defense, malware analysis, forensics, and incident response. They should also be certified in relevant fields, such as CISSP, CEH, or GIAC.
For larger organizations, the investment often pays off quickly. A dedicated threat hunter can significantly reduce the time to detect and respond to incidents. This means fewer successful breaches and lower overall risk. To start, consider promoting from within—train your existing security analysts in advanced hunting techniques. Alternatively, partner with a managed security service provider (MSSP) that offers threat hunting as part of its portfolio.
For more insights on building a resilient security team, check out our guide on cyber defense team building.
Integrating Threat Hunting into Your Cyber Defense Strategy
Once you have a threat hunter on board, integration is key. They should work closely with your incident response team, sharing findings and improving detection rules. Regular hunting sessions—whether daily, weekly, or monthly—should be scheduled based on your risk profile. Additionally, threat hunters can help refine your security monitoring by identifying gaps in coverage.
Another critical aspect is collaboration. Threat hunters should feed their insights into your broader security operations center (SOC). This creates a feedback loop: hunting reveals new indicators of compromise (IoCs), which are then used to update detection signatures. Over time, this continuous improvement makes your entire defense more robust.
Learn more about optimizing your SOC with our article on SOC optimization tips.
The Future of Threat Hunting: A Core Defense Component
As cyberattacks grow in frequency and sophistication, the role of the threat hunter will become indispensable. Already, industry surveys show that organizations with dedicated hunters detect breaches 50% faster than those without. In the coming years, we can expect threat hunting to evolve with artificial intelligence and machine learning, automating some aspects while still relying on human intuition.
For now, the message is clear: waiting for an attack to happen is no longer viable. By embracing proactive threat hunting, businesses can shift from damage control to genuine prevention. Whether you hire in-house or outsource, the investment in a threat hunter is an investment in your organization’s future security.
For more details on implementing advanced security measures, read our resource on advanced cybersecurity measures.


 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Infosecurity2 months ago
Infosecurity2 months ago
 Social Media2 months ago
Social Media2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Social Media2 months ago
Social Media2 months ago