Come Fly with Me: Securing the Drone — Why Urban UAS Safety Matters Now
Drones are no longer just military toys or hobbyist gadgets. They are becoming an integral part of modern life, from Amazon’s ambitious delivery plans to city-wide surveillance and infrastructure inspections. But as these unmanned aircraft systems (UAS) fill our skies, a critical question emerges: are we prepared for the drone security risks that come with them? Without proper safeguards, the very technology designed to improve our lives could open the door to cyberattacks, privacy violations, and even physical danger.
Understanding the Drone Security Risks in Smart Cities
The Cloud Security Alliance (CSA), in partnership with the Securing Smart Cities initiative, recently released a report titled Establishing a Safe and Secure Municipal Drone Program. This document highlights a sobering reality: drone technology is advancing faster than the safety measures needed to protect it.
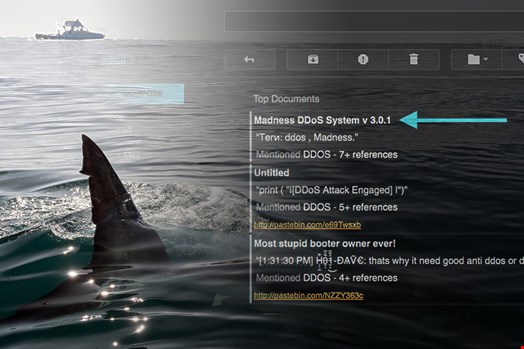
Brian Russell, co-author of the report and Chair of CSA’s IoT Working Group, notes that “drones will play an important and even critical role in the smart city environment.” Yet, the same connectivity that makes drones useful also makes them vulnerable. Hackers could gain control of a drone mid-flight, steal sensitive data, or cause crashes. Privacy concerns also loom large, as drones equipped with cameras can surveil public spaces without consent.
Key Challenges in Drone Cybersecurity
The report identifies several pressing challenges. First, the airspace where drones operate remains largely unregulated, with global guidelines still in their infancy. Second, drone manufacturers have historically neglected security during the development phase. Additionally, multiple integration points within a city-wide drone system—including cloud-based software—can serve as attack vectors. New, unproven algorithms for automated operations further complicate the picture.
Other issues include the anonymity of drone pilots, making it difficult to identify or locate operators, and the rapid proliferation of consumer drones that must share airspace with municipal fleets. As drones gain approval for Beyond Line of Sight (BLOS) operations, security engineers must plan now to counter future threats.
How to Secure a Municipal Drone Program
To address these drone security risks, the CSA report offers concrete recommendations. Cities should establish planning requirements that prioritize security from the outset. This includes integrated system design, acquisition security, and rigorous testing before deployment.
Mohamad Amin Hasbini, a board member of Securing Smart Cities, warns: “The mass adoption of drones by cities implies that thousands of programmable connected mobile devices will operate in the streets, above them, and below them. From a security perspective, this guarantees potential disasters if any system becomes compromised.” His message is clear: proactive measures are essential, not optional.
Best Practices for UAS Safety
For a successful municipal drone program, organizations must integrate security into every stage of the lifecycle. This means adopting methodical security practices during manufacturing, enforcing strict software programming standards, and ensuring ongoing monitoring and response capabilities. Governments and regulatory bodies also bear significant responsibility—they must set realistic yet strict guidelines that all stakeholders follow.
Building on this, cities can look to existing frameworks like those from the National Institute of Standards and Technology (NIST) for guidance. By learning from other sectors, such as the Internet of Things (IoT) and cloud computing, urban planners can avoid repeating past mistakes.
The Future of Drones in Urban Environments
Despite the risks, the potential of drones remains immense. They can conduct dull, dirty, or dangerous work—inspecting bridges, monitoring traffic, surveying wildlife, and supporting search and rescue missions. However, as the CSA report underscores, safety and security must keep pace with innovation.
Therefore, the path forward requires collaboration between manufacturers, regulators, and city officials. Software programming must be treated as a security priority from the development phase. At the same time, public awareness campaigns can help citizens understand both the benefits and the risks. As one expert put it, “Drones in the sky, drones in the sea, drones on land. But are we ready?”
In conclusion, the future of UAS could be extremely bright—but only if we address drone security risks head-on. By following the guidelines set forth by organizations like the CSA, we can ensure that drones serve as tools for progress, not vectors for chaos. So, as Sinatra sang, “Come fly with me”—but only when it’s secure. For more insights, check out our guide on smart city cybersecurity and IoT security best practices.


 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Infosecurity2 months ago
Infosecurity2 months ago
 Social Media2 months ago
Social Media2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Social Media2 months ago
Social Media2 months ago