How to Recover From a Cyber-Attack: A Step-by-Step Playbook for Organizational Resilience
No organization is completely immune to cyber threats. Even the most advanced defenses can fail. Therefore, building a robust cyber-attack recovery plan is no longer optional—it is essential for long-term survival. This article outlines a practical, six-stage recovery flow that can help your organization bounce back quickly and effectively after a cybersecurity breach.
Why Many Organizations Struggle with Cyber-Attack Recovery
Recovering from a cyber-attack is often chaotic and stressful. Many companies lack clear procedures, leading to delayed responses and increased damage. Common pitfalls include poor communication, insufficient backups, and a lack of defined roles. As a result, recovery times stretch from days to weeks, costing millions in lost revenue and reputational harm.
Building on this, organizations that treat recovery as an afterthought often face regulatory fines and legal consequences. A proactive approach to cyber-attack recovery is critical to minimize these risks.
The Six-Stage Recovery Planning Flow
Thibault Williams from TMW Resilience shares a structured framework that any organization can adapt. This flow moves from initial detection to full restoration, ensuring no step is overlooked.
Stage 1: Detection and Assessment
The moment a breach is suspected, rapid detection is key. This involves identifying the attack vector, affected systems, and the scope of data compromise. Use automated monitoring tools and a dedicated incident response team to speed up this process.
Stage 2: Containment
Once identified, immediately isolate compromised systems to prevent lateral movement. Disconnect affected servers, revoke compromised credentials, and block malicious IPs. Quick containment reduces the blast radius and limits data loss.
Stage 3: Eradication
Remove the threat from your environment. This includes deleting malware, patching vulnerabilities, and closing backdoors. A thorough eradication step prevents re-infection and ensures the attacker cannot regain access.
Stage 4: Recovery
Restore systems from clean backups, verify data integrity, and bring services back online gradually. Prioritize critical business functions first. Test each restored component before full deployment to avoid introducing new issues.
Stage 5: Post-Incident Analysis
After recovery, conduct a detailed review. What went wrong? What worked well? Document lessons learned and update your incident response plan accordingly. This step strengthens future defenses and improves cyber-attack recovery speed.
Stage 6: Communication and Reporting
Inform stakeholders, customers, and regulators as required by law. Transparent communication builds trust and demonstrates accountability. Prepare a clear narrative about the incident, the response, and the steps taken to prevent recurrence.
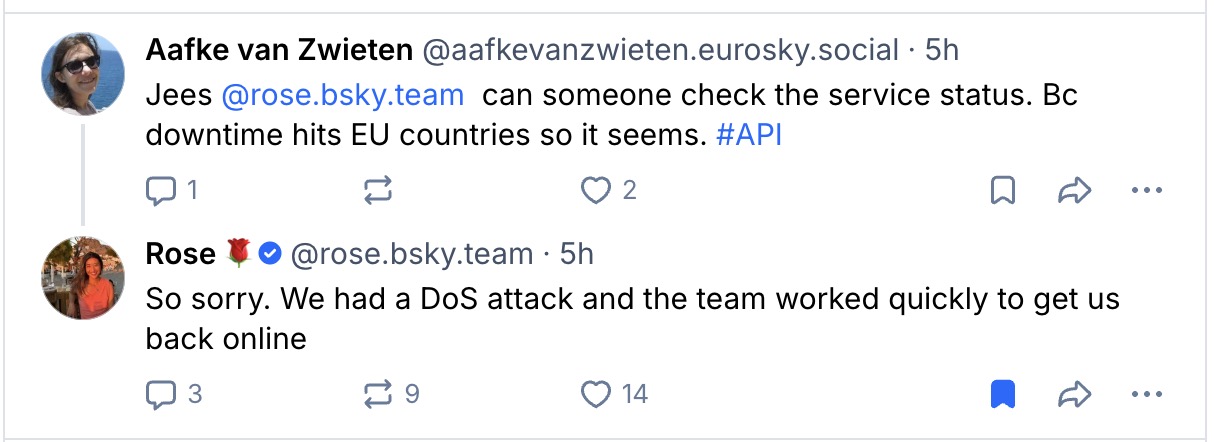
Real-Life Examples of Successful Recovery
Several organizations have turned cyber crises into opportunities for improvement. For instance, a global logistics firm faced a ransomware attack that shut down its shipping systems. By following a structured recovery flow, they restored operations within 48 hours, maintaining customer confidence. Another example is a healthcare provider that detected a breach early, contained it rapidly, and used post-incident analysis to overhaul its security architecture. These cases highlight the value of preparation and a disciplined recovery process.
On the other hand, companies that neglect planning often suffer prolonged outages and permanent reputational damage. This underscores why incident response planning must be a boardroom priority.
How to Assess Your Current Recovery Readiness
Not sure where your organization stands? Start by evaluating your existing procedures against the six-stage flow. Identify gaps in detection, containment, or communication. Conduct tabletop exercises to test your team’s response under pressure. Finally, invest in cyber resilience strategy training for all employees, from IT staff to executives.
In addition, consider partnering with external experts like TMW Resilience for tailored guidance. Their practical sessions provide actionable insights that can transform your recovery capabilities.
Conclusion: Make Recovery a Core Pillar
Cyber-attack recovery is not a one-time project—it is an ongoing commitment. By adopting a structured playbook, you reduce downtime, protect your brand, and build long-term resilience. Start today by reviewing your current plan and taking the first step toward a more secure future.
For more resources, explore our guide on cybersecurity best practices to complement your recovery efforts.

 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Infosecurity2 months ago
Infosecurity2 months ago
 Social Media2 months ago
Social Media2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Social Media2 months ago
Social Media2 months ago








