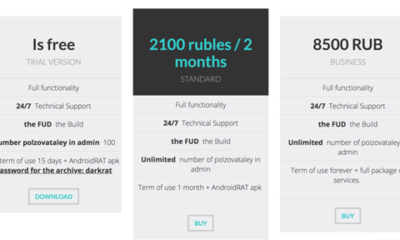

Dark RAT Malware: Inside the Android Remote Access Trojan Targeting Victims Worldwide Cybercriminals are constantly evolving their tactics, and the Dark RAT malware is a prime...


The Domain Name and Its Role in Cyber Forensics: Unmasking Digital Crime When you type a website address into your browser, the Domain Name System (DNS)...


Navigating the Security Challenges of Enterprise Container Adoption Over the past half-decade, the shift toward enterprise container adoption has transformed how organizations deploy software. From the...


Data Centre Security Checklist: 4 Critical Steps to Protect Your Digital Brain Modern organizations depend on data centres as the central hub for storing sensitive information,...


World Cybersecurity Congress 2017: A Day of Revelations and Future Directions The World Cybersecurity Congress 2017, held at Islington’s Business Design Centre, brought together experts from...

GDPR Compliance: Is It Becoming Mission Impossible for Businesses? The question of GDPR compliance challenges continues to dominate conversations across the information security industry. As the...


The Rise of the Threat Hunter: Proactive Cyber Defense for Modern Businesses Cyberattacks are no longer a question of if, but when. For many organizations, the...


SecuriTay 6: Key Takeaways from Abertay University’s Premier Hacker Conference On a stormy February day, I braved the winds of Storm Doris to travel north to...


Wendy Nather: Why the Cybersecurity Industry Must Rethink Its Approach At the RSA Conference 2017 in San Francisco, one voice stood out among the crowd: Wendy...


Digesting the Diversity of Data Breaches: Verizon’s 16 Scenarios and How to Tackle Them Data breaches have become one of the most pressing concerns for businesses...