

‘We’ll Always Have Paris’: Key Takeaways from ISSE Conference 2016 on Digital Identity The 17th annual ISSE Conference 2016 took place in the heart of Paris,...


How to Handle Security Stakeholders: Avoid These Common Pitfalls and Build Trust Managing a cybersecurity initiative is no small feat. IT and security leaders must collaborate...


Everything You Need to Know About RDNH and Protecting Your Business Domain Your domain name is more than just a web address — it’s your digital...


Closing the Gender Gap in Cybersecurity: A Path Forward The cybersecurity industry faces a pressing challenge: a severe shortage of skilled professionals. With predictions of 1.5...


Dr Jessica Barker: Three Critical Pitfalls That Undermine Security Awareness Cyber Security Awareness Month has just wrapped up, and the headlines were filled with massive breaches—from...


Will AI and Machine Learning Define the Future of Your Company? Artificial intelligence and machine learning are no longer futuristic concepts. They are actively reshaping how...


The Mirai Botnet and the IoT Awakening: Why Security Can No Longer Be an Afterthought The Mirai botnet IoT security wake-up call arrived with brutal clarity...


EU Cybersecurity Rules: Why Global Regulators Must Act Now on Digital Resilience The European Union’s landmark agreement on cybersecurity rules has sent a clear signal to...


Chris Inglis on Insider Threats, Snowden, and the Power of Behavioral Analytics When most people picture a cybersecurity discussion, the British Museum probably doesn’t come to...
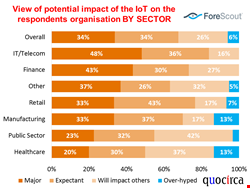

IoT Deployments Often Rely on Isolated Networks and Sub-Nets: How to Secure the Expanding Attack Surface The Internet of Things (IoT) promises to revolutionise business processes,...