How Neustar’s Real-Time Expertise Powers Next-Generation IoT Security Solutions
The explosive growth of connected devices presents both unprecedented opportunities and significant security challenges. As organizations worldwide embrace the Internet of Things, the demand for robust IoT security solutions has never been more critical. One company positioning itself at the forefront of this transformation is Neustar, leveraging nearly two decades of real-time information services expertise to address the complex security needs of tomorrow’s connected world.
From Telephony to IoT Security Solutions: Neustar’s Evolution
Building on its foundational experience managing the US Number Portability Administration Center (NPAC), Neustar developed unparalleled capabilities in handling high-volume, real-time information processing. This seemingly mundane telephony service required the company to act as a neutral intermediary between service providers, ensuring seamless number transfers while maintaining data integrity across millions of transactions.
However, this background proved invaluable as the company expanded its horizons. The infrastructure requirements for managing real-time telephony data transfers mirror many challenges facing modern IoT security solutions. What worked for telephone numbers now applies to device authentication, location verification, and threat detection across vast networks of connected devices.
In addition, Neustar’s acquisition strategy has strengthened its position considerably. The 2010 purchase of Quova brought IP geolocation capabilities with claimed 99.1% accuracy, while the 2015 acquisition of MarketShare added digital marketing measurement expertise to their portfolio.
Real-Time Threat Detection and Device Verification
The connection between IP geolocation and security becomes apparent when considering suspicious device behavior. Traditional security models struggle with the “what is that device doing in that location” question that modern IoT environments constantly present. This is where Neustar’s real-time information services create substantial value.
Consider the authentication challenges facing IoT deployments. As devices communicate machine-to-machine (M2M) without human intervention, verification must happen instantaneously. Delays in authentication or location verification can compromise entire networks or create service disruptions that cascade across interconnected systems.
Therefore, the ability to provide sub-second verification of device identity and expected location becomes a cornerstone of effective IoT security solutions. Neustar’s infrastructure, battle-tested through years of telephony operations, offers the reliability and speed these applications demand.
DNS Infrastructure as IoT Security Foundation
The domain name services (DNS) business represents another crucial element in Neustar’s IoT security strategy. Managing authoritative DNS services for the .NET domain and enterprise customers through Ultra DNS provided the company with deep insights into network traffic patterns and potential vulnerabilities.
DNS infrastructure faces constant threats from distributed denial of service (DDoS) attacks, particularly as IoT device networks expand. Using Arbor hardware, Neustar built comprehensive DDoS protection capabilities that evolved into their SiteProtect service in 2011.
This experience proves particularly relevant as IoT deployments create new attack vectors. Research indicates that IoT devices often lack robust security protocols, making them attractive targets for cybercriminals seeking to build massive botnets for DDoS attacks. Organizations need DNS-level protection that can identify and mitigate these threats before they impact critical systems.
As a result, Neustar competes directly with established players like Akamai, which acquired Prolexic to strengthen its DDoS protection offerings. However, Neustar’s unique combination of real-time processing expertise and comprehensive device intelligence creates differentiated value propositions.
European Market Opportunities for IoT Security
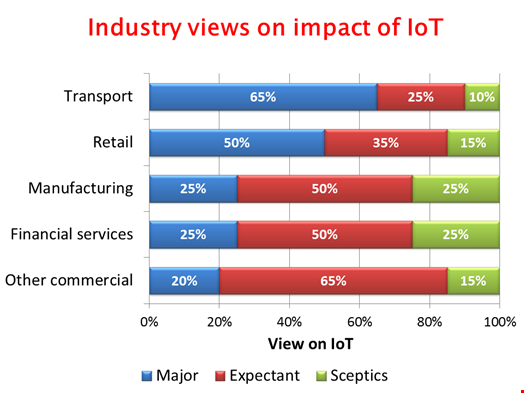
Recent Quocirca research highlighted significant concerns about IoT implementation, particularly regarding the expanded attack surface these technologies create. UK businesses recognize IoT benefits but simultaneously worry about security implications, creating substantial market opportunities for proven IoT security solutions.
The European market presents unique advantages for Neustar’s expansion strategy. GDPR compliance requirements align well with the company’s experience handling sensitive consumer data while maintaining strict privacy standards. Their track record of operating as a neutral intermediary between competing organizations translates effectively to European regulatory environments that prioritize data protection and competitive neutrality.
Furthermore, European organizations increasingly demand real-time performance monitoring and protection services to ensure IoT application reliability. This requirement matches perfectly with Neustar’s core competencies in high-volume, real-time information processing developed through decades of telephony operations.
The Future of Connected Device Protection
Looking ahead, the convergence of device authentication, location verification, and threat protection creates compelling opportunities for integrated security platforms. Organizations need solutions that can verify device identity, confirm expected behavior patterns, and respond to threats in real-time across thousands or millions of connected endpoints.
Neustar’s registry of things concept addresses this need by creating comprehensive databases of device characteristics and expected behaviors. Combined with their geolocation accuracy and DDoS protection capabilities, this approach offers holistic IoT security solutions that scale with organizational needs.
The transition from their US telephony focus toward European IoT markets represents a natural evolution of proven technologies. As connected device deployments accelerate across industries, organizations need partners with demonstrated expertise in managing complex, real-time information systems at massive scale.
In conclusion, Neustar’s unique heritage positions the company to address critical security challenges facing IoT implementations. Their combination of real-time processing expertise, accurate geolocation services, and comprehensive DNS protection creates valuable differentiation in an increasingly competitive market. For European organizations evaluating IoT security strategies, Neustar’s proven track record offers compelling advantages in an uncertain threat landscape.


 CyberSecurity4 weeks ago
CyberSecurity4 weeks ago
 CyberSecurity4 weeks ago
CyberSecurity4 weeks ago
 Infosecurity4 weeks ago
Infosecurity4 weeks ago
 CyberSecurity4 weeks ago
CyberSecurity4 weeks ago
 CyberSecurity4 weeks ago
CyberSecurity4 weeks ago
 How To3 weeks ago
How To3 weeks ago
 CyberSecurity4 weeks ago
CyberSecurity4 weeks ago
 CyberSecurity4 weeks ago
CyberSecurity4 weeks ago