Two Americans Sentenced for Running Laptop Farms in North Korea’s $5 Million IT Worker Fraud
The North Korea fake IT worker scheme has resulted in significant prison sentences for two U.S. citizens who helped the isolated regime steal millions from American companies. On Wednesday, the U.S. Department of Justice announced that Kejia Wang and Zhenxing Wang, both residents of New Jersey, were sentenced to seven and a half years and nine years in prison, respectively.
These individuals played a critical role in enabling North Korean operatives to pose as remote IT employees for American firms. Their actions not only funneled money to Pyongyang but also exposed sensitive corporate data to foreign adversaries.
How the Laptop Farm Operation Worked
Between 2021 and 2024, the two men managed so-called “laptop farms” inside the United States. Kejia Wang oversaw a network of hundreds of computers, while Zhenxing Wang hosted laptops at his own home. This infrastructure allowed North Korean IT workers to connect remotely and appear as if they were living and working within the country.
In addition, the pair created shell companies with financial accounts linked to fake identities. These accounts received payments from unwitting U.S. employers, which were then transferred overseas. The scheme netted North Korea approximately $5 million, with the facilitators themselves receiving nearly $700,000 for their roles.
Identity Theft and National Security Risks
The North Korea fake IT worker scheme involved stealing the identities of more than 80 Americans. According to the DOJ, these fake workers secured jobs at over 100 U.S. corporations, including several Fortune 500 companies. Beyond collecting salaries, the operatives sometimes stole trade secrets and source code.
In one alarming case, the fake IT workers accessed data under export control from an unnamed California-based AI company. John A. Eisenberg, the DOJ’s assistant attorney general for National Security, stated: “The ruse placed North Korean IT workers on the payrolls of unwitting U.S. companies and in U.S. computer systems, thereby harming our national security.”
Rewards for Information
To combat similar threats, the U.S. government announced rewards of up to $5 million for information that could help counter these schemes. This includes data on nine individuals who allegedly collaborated with Kejia Wang and Zhenxing Wang. The DOJ encourages anyone with knowledge of such operations to come forward.
Broader Context of North Korean Cyber Crime
This sentencing is the latest legal action against a wide-ranging campaign by North Korea to infiltrate Western companies. Alongside major crypto thefts exceeding $2 billion last year alone, the regime uses such fraud to fund its weapons programs and bypass heavy international sanctions.
Companies and recruiters have developed creative countermeasures. For instance, some interviewers ask suspected North Korean applicants to insult Kim Jong Un—an act that is illegal in the country. In a recent viral video, a job applicant fumbled and eventually hung up when asked to say the leader is a “fat ugly pig.”
For more insights on cybersecurity threats, check out our guide on protecting your business from remote worker fraud. Additionally, learn about how North Korea uses cyber operations to evade sanctions.
What This Means for U.S. Companies
Businesses must remain vigilant when hiring remote IT workers. The North Korea fake IT worker scheme demonstrates how sophisticated these operations can be. Verifying identities through video calls, checking for inconsistencies in resumes, and using background screening services are essential steps.
Furthermore, companies should monitor for unusual network activity or attempts to access sensitive data without authorization. The DOJ’s action sends a clear message: facilitators of such schemes will face severe consequences.


 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 Infosecurity2 months ago
Infosecurity2 months ago
 Social Media2 months ago
Social Media2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
 CyberSecurity2 months ago
CyberSecurity2 months ago
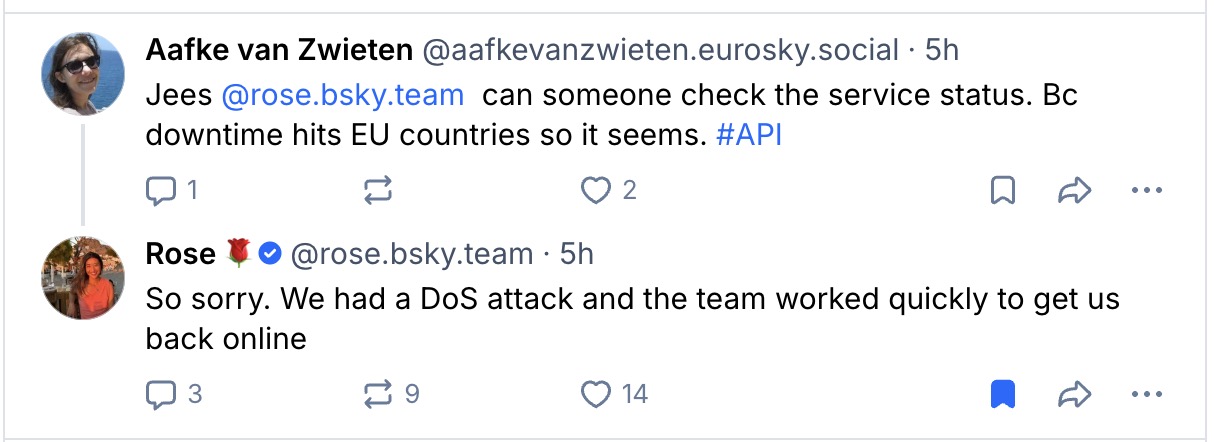
 Social Media2 months ago
Social Media2 months ago